Jan 11, 2016 Windows 10 Remote Desktop (RPD) using Microsoft Account (aka Live account) Log on as admin user with RDP Create a local (not Microsoft account) account with the name that would be before the @ (i.e. Qwerty if the MS email were qwerty@outlook.com) Give to the created local user the “Remote Desktop Users” rights. Jul 11, 2017 Go to the Start menu or open a Run prompt (Windows Key + R) and type “secpol.msc” to open the Local Security Policy menu. Once there, expand “Local Policies” and click on “User Rights Assignment.” Double-click on the “Allow log on through Remote Desktop Services” policy listed on the right. The issue with multiple Remote Desktop Sessions on Windows 10 and 8. Attempting to initiate a second Remote Desktop session will cause any users working locally on the machine or logged in through an existing RDP session to be kicked out. The issue is not a result of the technical capabilities of Windows 10 but rather with the license agreement. In this Windows tutorial, I will show how Windows administrators can create a local Windows user account and allow user account to access Windows PC remotely using Remote Desktop Connection. This is a two step task for Windows admins; creating Windows user and granting remote access permission to the user on that Windows server.
Symptoms
If you are not an administrator and try to use the Remote Desktop Connection tool, you may receive the following error message:
The local policy of this system does not permit you to logon interactively.
Cause
This issue occurs because the user account is not a member of the local Remote Desktop Users group.
Resolution
To have us resolve this issue for you, go to the 'Fix it for me' section. If you prefer to fix this problem yourself, go to the 'Let me fix it myself' section.
Fix it for me
To fix this problem automatically, click the Fix it button or link. Click Run in the File Download dialog box, and follow the steps in the Fix it wizard.
Notes
Type the user account in the Users box during the installation of the Fix it solution.
To add a domain user account to the local Remote Desktop Users group, use the following format:
DomainUsernameTo add a local user account to the local Remote Desktop Users group, use the following format:
Username or .UsernameTo add multiple user accounts to the local Remote Desktop Users group,use the semicolon(;) character as the separator.For example:
Username1;Username2This wizard may be in English only. However, the automatic fix also works for other language versions of Windows.
If you are not using the computer that has the problem, save the Fix it solution to a flash drive or a CD and then run it on the computer that has the problem.
Then, go to the 'Did this fix the problem?' section.
Let me fix it myself
To resolve this issue, add allowed users to the Remote Desktop Users list:
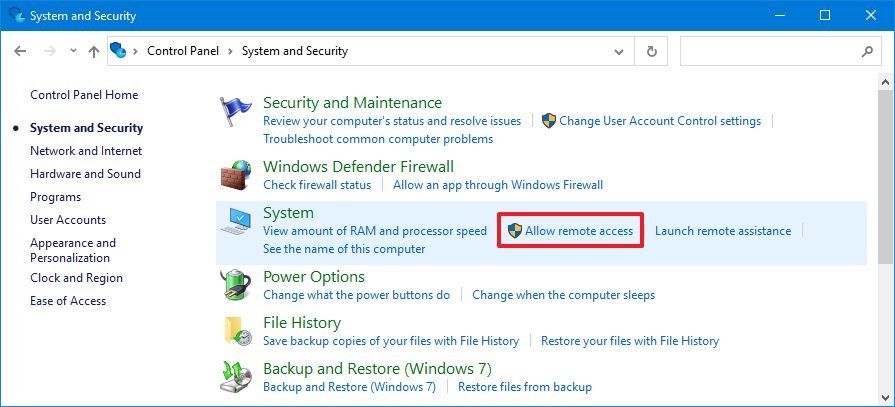
Click Start, point to Settings, and then click Control Panel.
Double-click System, and then on the Remote tab, click Select Remote Users.
Click Add type in the user account name, and then click OK.
If you are adding more than one user name, use a semicolon to separate the names.

Note: Adding users to the Remote Desktop Group requires that you are logged on through an administrator account.
Also, make sure that the Remote Desktop Users group has sufficient permissions to log on through Terminal Services. To do this, follow these steps:
Click Start, click Run, type secpol.msc, and then click OK.
Expand Local Policies, and then click User Rights Assignment.
In the right pane, double-click Allow logon through Terminal Services. Make sure that the Remote Desktop Users group is listed.
Click OK.
In the right pane, double-click Deny logon through Terminal Services. Make sure that the Remote Desktop Users group is not listed, and then click OK.
Close the Local Security Settings snap-in.
Did this fix the problem?
Check whether the problem is fixed. If the problem is fixed, you are finished with this section. If the problem is not fixed, you can contact support.
We would appreciate your feedback. To provide feedback or to report any issues with this solution, please leave a comment on the 'Fix it for me' blog or send us an
email.
Applies to
- Windows 10
Describes the best practices, location, values, policy management, and security considerations for the Allow log on through Remote Desktop Services security policy setting.
Reference
This policy setting determines which users or groups can access the logon screen of a remote device through a Remote Desktop Services connection. It is possible for a user to establish a Remote Desktop Services connection to a particular server but not be able to log on to the console of that same server.
Constant: SeRemoteInteractiveLogonRight
Possible values
- User-defined list of accounts
- Not Defined
Best practices
- To control who can open a Remote Desktop Services connection and log on to the device, add users to or remove users from the Remote Desktop Users group.
Location
Computer ConfigurationWindows SettingsSecurity SettingsLocal PoliciesUser Rights Assignment
Default values
By default, members of the Administrators group have this right on domain controllers, workstations, and servers. The Remote Desktops Users group also has this right on workstations and servers.The following table lists the actual and effective default policy values. Default values are also listed on the policy’s property page.
Remote Desktop Help Windows 10
| Server type or GPO | Default value |
|---|---|
| Default Domain Policy | Not Defined |
| Default Domain Controller Policy | Not Defined |
| Domain Controller Local Security Policy | Administrators |
| Stand-Alone Server Default Settings | Administrators Remote Desktop Users |
| Domain Controller Effective Default Settings | Administrators |
| Member Server Effective Default Settings | Administrators Remote Desktop Users |
| Client Computer Effective Default Settings | Administrators Remote Desktop Users |
Policy management
This section describes different features and tools available to help you manage this policy.
Group Policy
To use Remote Desktop Services to successfully log on to a remote device, the user or group must be a member of the Remote Desktop Users or Administrators group and be granted the Allow log on through Remote Desktop Services right. It is possible for a user to establish an Remote Desktop Services session to a particular server, but not be able to log on to the console of that same server.
To exclude users or groups, you can assign the Deny log on through Remote Desktop Services user right to those users or groups. However, be careful when you use this method because you could create conflicts for legitimate users or groups that have been allowed access through the Allow log on through Remote Desktop Services user right.
For more information, see Deny log on through Remote Desktop Services.
A restart of the device is not required for this policy setting to be effective.
Any change to the user rights assignment for an account becomes effective the next time the owner of the account logs on.
Group Policy settings are applied through GPOs in the following order, which will overwrite settings on the local computer at the next Group Policy update:
- Local policy settings
- Site policy settings
- Domain policy settings
- OU policy settings

Security considerations
This section describes how an attacker might exploit a feature or its configuration, how to implement the countermeasure, and the possible negative consequences of countermeasure implementation.
Vulnerability
Any account with the Allow log on through Remote Desktop Services user right can log on to the remote console of the device. If you do not restrict this user right to legitimate users who must log on to the console of the computer, unauthorized users could download and run malicious software to elevate their privileges.
Countermeasure
For domain controllers, assign the Allow log on through Remote Desktop Services user right only to the Administrators group. For other server roles and devices, add the Remote Desktop Users group. For servers that have the Remote Desktop (RD) Session Host role service enabled and do not run in Application Server mode, ensure that only authorized IT personnel who must manage the computers remotely belong to these groups.
Caution: For RD Session Host servers that run in Application Server mode, ensure that only users who require access to the server have accounts that belong to the Remote Desktop Users group because this built-in group has this logon right by default.
Alternatively, you can assign the Deny log on through Remote Desktop Services user right to groups such as Account Operators, Server Operators, and Guests. However, be careful when you use this method because you could block access to legitimate administrators who also belong to a group that has the Deny log on through Remote Desktop Services user right.
Potential impact
Local Security Settings Remote Desktop Windows 10
Removal of the Allow log on through Remote Desktop Services user right from other groups (or membership changes in these default groups) could limit the abilities of users who perform specific administrative roles in your environment. You should confirm that delegated activities are not adversely affected.
Related topics
